Security Information and Event Management (SIEM) for businesses
Security Information and Event Management (SIEM) is a cybersecurity platform that collects and analyses data from across an organisation’s systems to identify suspicious activity and threats, and generate alerts.
It serves as the cybersecurity HQ for organisations with extensive digital estates, providing security teams with global visibility into all systems from a single place. While powerful, SIEMs are resource-intensive and costly; complex deployments can exceed £1 million per year.
This article explains what a SIEM is, how it works, who it’s for, the available designs, and its pricing.
Contents:
- What is the key security problem that SIEM solves?
- How does SIEM work?
- SIEM design for businesses
- Which businesses need a SIEM and why
What is Security Information and Event Management (SIEM)?
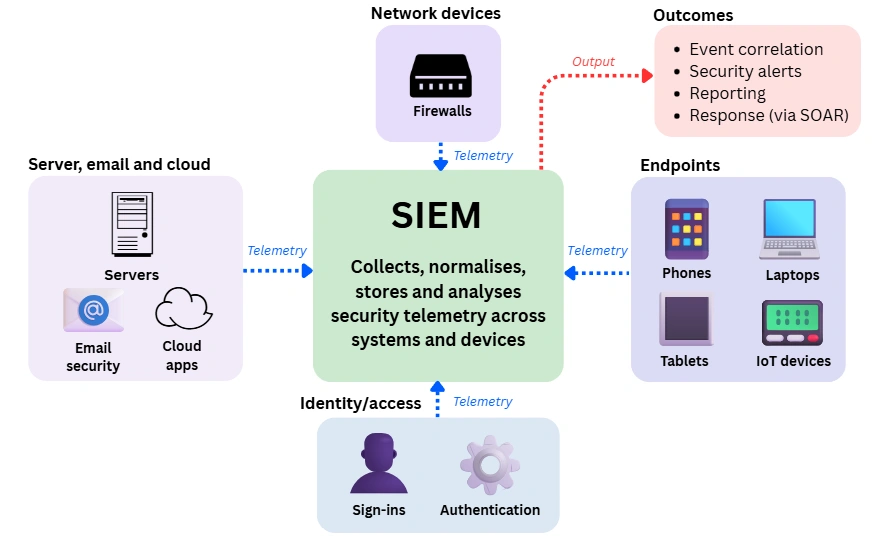
A SIEM is an enterprise cybersecurity platform that collects, cleans, stores and analyses security data from across an organisation’s systems, including firewalls, gateways, endpoints, servers and cloud applications.
It is designed to give security teams visibility and control across the entire digital estate from a single, centralised platform. A SIEM consists of two core components:
- Security Information (SI): A central data store that collects and organises security data from across all systems (such as servers, endpoints, network devices and cloud applications). This data can be searched, analysed, and reported over time to support investigations, audits and compliance.
- Event Management (EM): The real-time analysis layer that correlates events to detect suspicious activity and generate alerts. It leverages historical data stored in the SI component to provide security teams with visibility across all systems simultaneously.
Without a SIEM, organisations with large, complex, or sensitive environments often lack the visibility, audit trails, and analytical capabilities needed to detect threats early or to meet regulatory and compliance requirements such as ISO 27001, GDPR, and PCI DSS.
They would be unable to demonstrate effective security controls to customers, auditors, and regulators, which would limit their ability to bid for major public-sector or enterprise contracts.
That said, SIEM is not suitable for every organisation. It requires significant time, expertise and ongoing investment to deploy and operate, making it one of the most resource-intensive cybersecurity solutions. For many businesses, this means carefully weighing SIEM against simpler security approaches that better align with their size, risk profile, and budget.
What is the key security problem that SIEM solves?
SIEM exists to solve a fundamental cybersecurity problem: security data management. Modern organisations generate vast amounts of security data, but without a central system, it is difficult to use that data to reliably detect threats and respond before damage occurs.
This is because IT environments have grown steadily more complex over time. Most organisations now operate a mix of on-premise systems, cloud services, remote users and third-party applications, all generating fragmented logs and alerts across hundreds of tools and platforms.
SIEM platforms emerged to address this fragmentation by centralising log management and supporting compliance reporting. As cyber threats became more frequent and sophisticated, SIEMs evolved into core operational security systems rather than just reporting tools.
Its widespread adoption reflects how essential it has become for organisations that need visibility, control and accountability across their digital estate.
In practice, the larger or more complex the organisation, the greater the need for SIEM to solve the following issues:
- Security data fragmentation: Security data is scattered across many systems, making it hard to form an accurate, end-to-end view of activity.
- Missed threat detection: Genuine threats are buried in large volumes of logs, alerts and background noise.
- Slow response times: Without real-time correlation and alerting, security teams struggle to detect and respond quickly enough.
- Difficulty in investigations: Incident investigations are slow and manual when data exists in multiple tools and formats.
- Proving compliance: Demonstrating compliance is challenging without centralised logging, audit trails and reporting.
- Historical trail: Organisations often lack the historical data needed for forensic analysis and post-incident review.
- Overwhelmed security teams: Small teams face alert fatigue and limited visibility, reducing effectiveness.
By centralising security data and correlating events in real time, SIEM turns raw information into actionable insight. This enables organisations to detect threats earlier, respond faster, and manage security more effectively.
How does SIEM work?
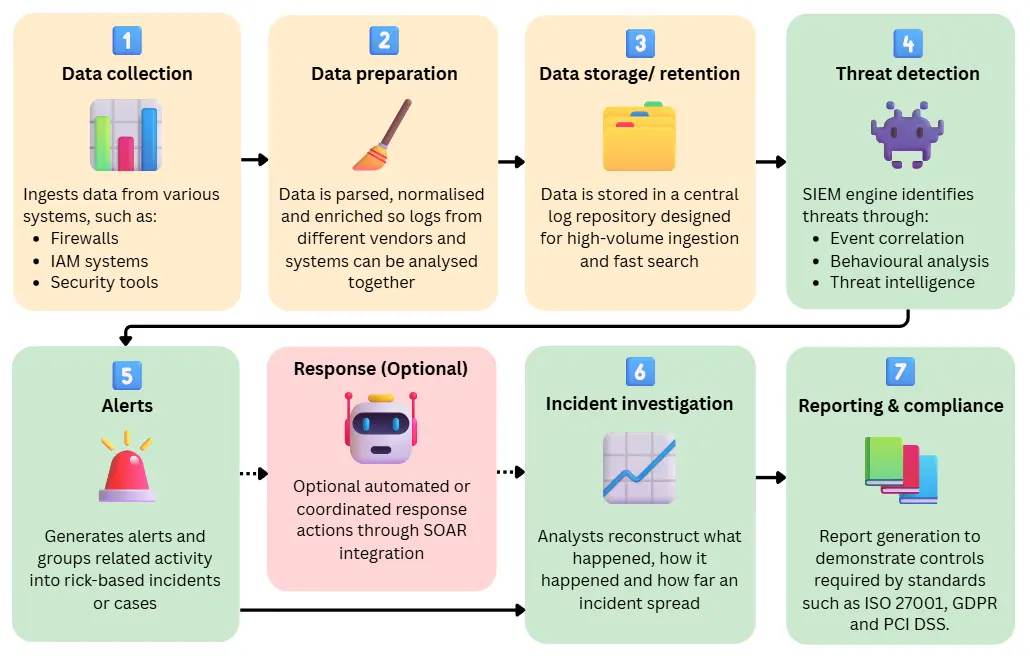
A SIEM works by pulling data from across an organisation, transforming it into a common structure, analysing it for signs of malicious or risky behaviour, and then enabling security teams to investigate, respond and report effectively.
At a high level, SIEM follows a clear, repeatable flow:
1. Data collection: Via APIs, agents, and log forwarders
A SIEM begins by ingesting data from across its wide area network, commonly:
- Server logs
- Network devices (firewalls, routers, switches, proxies)
- Identity and access management (IAM) systems (Conditional access, Single-Sign On, Multi-Factor Authentication rules)
- Cloud platforms
- SaaS applications
- Email security tools
- Specialist security products (Business antivirus solutions, Endpoint Detection and Response (EDR), vulnerability scanners)
Cloud-native SIEMs like Microsoft Sentinel rely heavily on API-based ingestion. At the same time, platforms such as Splunk and IBM QRadar support a mix of lightweight agents, log forwarders and network-based collection. The aim is broad coverage rather than deep analysis at this stage.
2. Data preparation: Parsing, normalisation and enrichment
Once ingested, raw data is parsed and normalised so logs from different vendors and systems can be analysed together.
This involves mapping raw fields into a common structure and aligning key attributes such as timestamps, usernames, IP addresses and actions using standard schemas like Common Event Format (CEF) or Elastic Common Schema (ECS).
The SIEM then enriches events (i.e. attaches additional context from sources it already has access to), turning raw log entries into security-relevant events. Enrichment commonly draws on:
- Asset context: Whether the asset is a user laptop, a production server, a domain controller or a cloud workload, as well as its business criticality and sensitivity.
- Identity context: Whether the activity was performed by a standard user, an administrator or a service account, and what level of access they normally have.
- Threat intelligence: Whether the IP address, domain or file involved is already associated with known malicious activity.
- Location context: Whether the activity originated from a normal location for that user or system, or from an unexpected country or region.
3. Data storage and retention
Normalised and enriched data is stored in a central log repository designed for high-volume ingestion and fast search. SIEM platforms are built to manage security data at scale while balancing performance, cost and retention requirements.
Most SIEMs use multiple storage tiers:
- Hot data: Recent events. Used for real-time detection and active investigation
- Warm or cold data: Lower-cost storage that remains searchable for historical analysis
- Archived data: Compressed, long-term storage for compliance and legal needs
Typical retention ranges include:
- Short-term retention: 30–90 days for operational monitoring
- Medium-term retention: 6–12 months for investigations and threat hunting
- Long-term retention: 1–7 years for cybersecurity compliance, audit and legal requirements
Data may be stored on-premise, in the cloud, or in a hybrid model. Regardless of deployment, this central log store becomes the authoritative record of security activity.
4. Event correlation and threat detection
The SIEM continuously analyses incoming data and correlates events across systems to identify patterns that indicate potential threats. Detection methods include:
- Rule-based correlation: Linking events across users, devices and systems. For example, multiple failed login attempts followed by a successful login from a new country and an immediate privilege change.
- Behavioural analysis: Identifying deviations from normal activity baselines. For instance, a user downloading large volumes of data at unusual hours from a new location.
- Threat intelligence matching: Comparing activity against known indicators of compromise, such as outbound network traffic communicating with a blacklisted IP address.
5. Alerting and incident prioritisation
When detection logic is triggered, the SIEM generates alerts and groups related activity into incidents or cases. Its primary role at this stage is to reduce noise and help analysts focus on signals that have the highest risk. Incidents are typically prioritised based on:
- Severity: Potential impact of the activity. For example, unusually large data downloads may indicate attempted data exfiltration.
- Confidence: Likelihood that the alert represents a real threat. The same data download may be lower risk if it originates from a known device and trusted location.
- Business impact: Importance of affected users, systems or data. This data theft on regulated systems carries a much higher risk due to compliance and financial penalties.
At this point, the SIEM has identified suspicious behaviour, correlated it across systems and presented it as a prioritised incident with relevant context.
SIEM-SOAR integration for automated response
The SIEM’s role largely ends once a threat has been detected, categorised and surfaced. A SIEM on its own typically does not take response actions, so for automated or coordinated response the SIEM needs to be integrated with a SOAR (Security Orchestration, Automation and Response) platform.
SOAR receives SIEM events and automatically triggers response actions via integrations (such as API connections or agents). Responses are executed by devices or platforms capable of enforcing changes, including:
- Firewalls/Next Generation Firewalls: Can block or restrict traffic based on rules (for example IP addresses, ports or destinations).
- IAM (Identity & Access Management platforms): Can deactivate accounts, revoke sessions, or require additional authentication (MFA).
- EDR (Endpoint Detection & Response platforms): Can isolate endpoints or stop processes via endpoint agents.
- Other controls: Cloud, server and email security tools can isolate workloads, restrict access, or block traffic to and from applications.
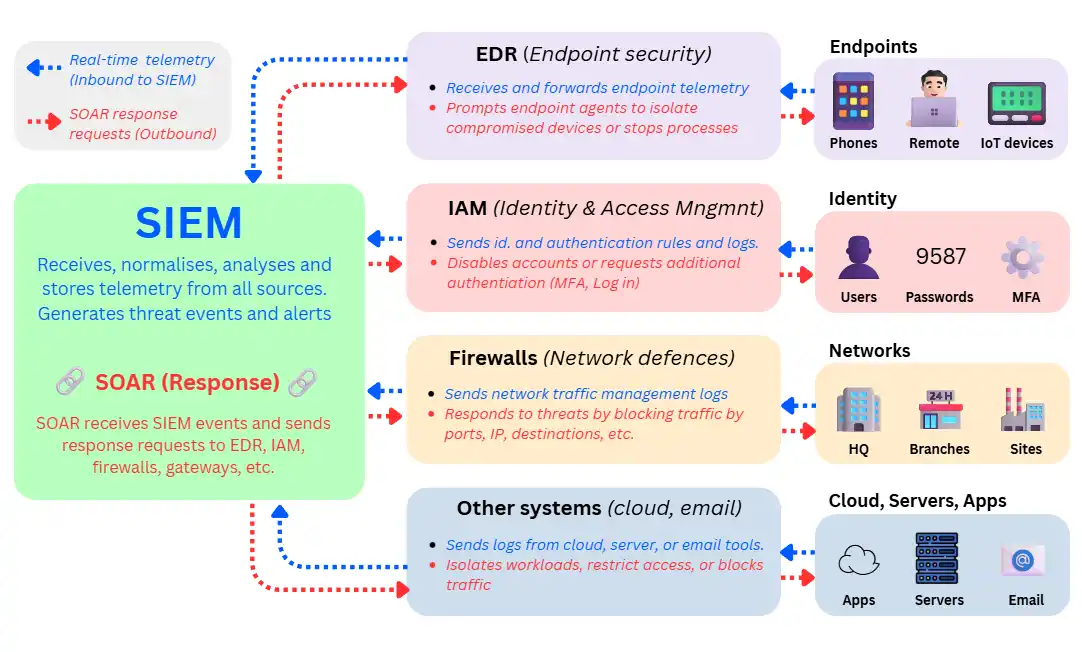
Many organisations that operate a SIEM pair it with SOAR as they come tightly integrated in cybersecurity solutions such as Microsoft Sentinel.
6. Investigation and analysis
SIEM investigation takes place both immediately after alerts are raised and over longer periods during incident response, threat hunting and post-incident review.
Security Operation Centre (SOC) analysts reconstruct what happened, how it happened and how far an incident spread. Core investigation capabilities include:
- Timeline analysis: Reconstructing event sequences across multiple systems to understand attack progression, such as tracing business email compromise to an initial login, followed by privilege escalation, lateral movement and data access over several days.
- Entity pivoting: Moving fluidly between event-related entities such as users, devices, IP addresses, sessions and cloud resources, in one single dashboard.
- Advanced search: Querying large volumes of normalised log data using structured queries and filters, such as searching months of authentication and endpoint logs to determine when malicious activity first began.
- Dashboards and visualisations: Summarising incident scope, spread and impact in a way that supports decision-making and reporting. For instance, visualising which business units, data stores or regions were affected during an incident.
Because all relevant data is centralised and normalised, investigations can be carried out at scale without manually pulling logs from multiple tools. This is key because analysts of large networks work with millions to billions of events collected across weeks, months or years.
7. Reporting and compliance
Finally, SIEM supports governance, risk management and compliance through reporting and evidence generation.
Centralised logs, alert histories and investigation records make it easier to demonstrate monitoring, incident handling and data protection controls required by standards such as ISO 27001, GDPR and PCI DSS.
For many organisations, this compliance capability was the original reason for adopting SIEM, and it remains a core justification for its continued use.
SIEM architecture for businesses
SIEMs can be implemented using a variety of architectures depending on the scale and use cases they need to support. These designs are typically described across three layers (hosting, deployment, and operation) which together form the SIEM architecture:
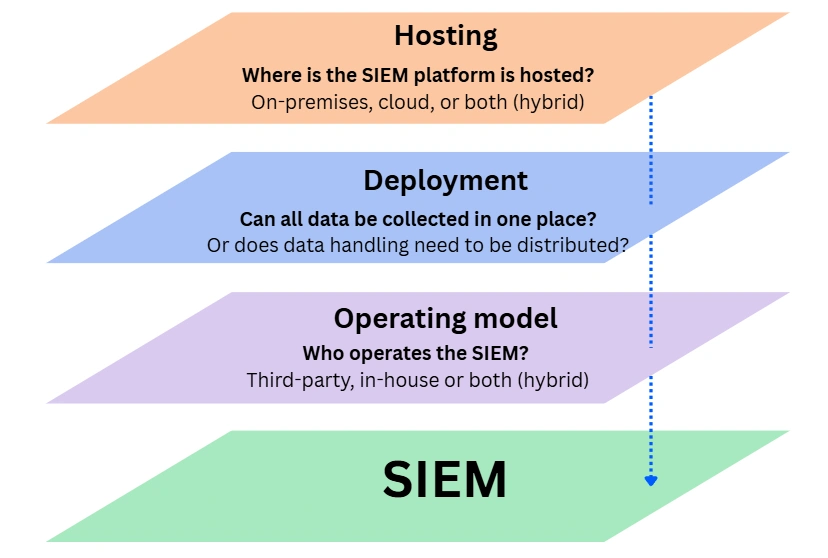
SIEM hosting models
Hosting models describe where the SIEM backend runs, including log storage, data processing and analytics. Most organisations collect data from both on-premises and cloud systems, so “hosting” refers to the SIEM platform itself, not the sources it connects to.
On-premise SIEM
Best for: Large organisations that already operate data centres and must keep security data on internal infrastructure.
The SIEM runs entirely on servers owned and managed by the organisation. Ingestion, storage and analysis take place within the internal network, under the organisation’s control. The trade-off is higher operational complexity and slower scalability.
Organisations operate on-premise SIEM because of:
- Strict data residency or sovereignty requirements
- Highly regulated environments (e.g. defence, finance, healthcare, critical infrastructure)
- Existing investment in on-prem infrastructure and in-house security teams
Cloud-native SIEM
Best for: SMEs looking for enterprise-grade security monitoring without managing infrastructure.
Here, the SIEM runs entirely in the cloud. Logs from both on-premises and cloud systems are forwarded to a managed platform using agents, connectors or APIs.
Cloud SIEM is ideal for smaller businesses because it:
- Scales easily with telemetry volume
- Reduces infrastructure and maintenance overhead
- Fits naturally with hybrid IT environments
Hybrid SIEM
Best for: Organisations that need to monitor both on-site systems and cloud services from a single place.
A hybrid SIEM keeps parts of the data pipeline on-premises (typically collection and/or short-term storage) while analytics and/or long-term retention run in the cloud.
In practice, many large or multi-site organisations use a hybrid SIEM because it allows tighter control over sensitive on-site telemetry while retaining the flexibility of cloud analytics and retention. Other reasons include:
- Certain logs cannot leave the site
- Latency or bandwidth constraints
- Cloud adoption is gradual
SIEM deployment models
SIEM deployments also need to be adapted to the telemetry sources being monitored. For example, collecting and analysing data from a busy Next-Generation Firewall or cloud application is very different from processing data from a handful of endpoints.
SIEM should be deployed so telemetry can be collected reliably. Ideally, it is centralised, but at larger scale, collection often needs to be distributed to avoid bottlenecks and resilience issues.
Centralised SIEM
Best for: Small to mid-sized environments and cloud-native deployments.
This is the ideal setup; all telemetry is forwarded to a central SIEM over existing links. It is typically feasible when:
- Networks are simple: A single office, a small number of sites, or workloads primarily hosted in one cloud environment.
- Data volumes are manageable: A few gigabytes of security data per day from firewalls, cloud services and a modest number of endpoints.
- Sites have reliable connectivity: Fibre-based business leased lines, private point-to-point or resilient business WAN connectivity where outages are unlikely
As organisations grow, either the links used to transmit telemetry must be upgraded (e.g., through Business Ethernet, MPLS or SD-WAN solutions), or SIEM data handling capabilities need to be placed closer to the sources.
SIEM with distributed data collection
Best for: Multi-site enterprises, distributed data centres or businesses operating across multiple jurisdictions.
Here, collection and preprocessing are distributed closer to telemetry sources (e.g., branch offices or regional data centres) via collectors or agents. These can batch, compress, filter and buffer logs before forwarding them to a central SIEM for correlation and analysis.
This provides:
- Reduced bandwidth usage: By batching, compressing or filtering high-volume logs before forwarding
- Improved resilience: Logs can be buffered locally during WAN outages and forwarded when connectivity returns
- Lower latency and operational impact: High-frequency sources can write locally without depending on real-time business broadband speeds.
SIEM operating models
The final part of the SIEM architecture is the role of the team responsible for monitoring, investigation, and day-to-day operations. There are two main approaches:
In-house SIEM
Best for: Large businesses with strict compliance and data security requirements.
The organisation’s security or IT team operates the SIEM, handling alert triage, investigations and reporting. This is typically associated with on-premises or hybrid deployments, and can be resource and cost-intensive, requiring sufficient in-house skills and capacity.
Managed SIEM (MSSP-led)
Best for: SMEs seeking predictable costs
Some organisations outsource SIEM operations to a Managed Security Service Provider (MSSP). The SIEM is often cloud-based, with day-to-day monitoring, alert triage and sometimes investigation handled externally (often working closely with the internal team).
The trade-off is reduced direct control and dependence on the provider’s processes and expertise.
Why is SIEM essential for compliance?
Cyber regulations and standards do not mandate specific tools such as a SIEM. Instead, they require organisations to demonstrate consistent, well-governed security practices.
As environments grow in scale and complexity, maintaining a central, long-term record of security activity that can be audited and reported on becomes increasingly important.
Standards such as ISO 27001, PCI DSS, and SOC 2, along with regulations like GDPR, generally require organisations to demonstrate that security activities are logged, monitored, investigated and reported in a consistent and defensible way.
For many organisations, compliance reporting was an early driver for SIEM adoption and remains one of its most enduring and defensible use cases. Here’s how SIEM supports cybersecurity compliance across common standards and requirements:
- ISO 27001: Helps demonstrate that security controls are monitored and that incidents can be detected, investigated and explained over time.
- PCI DSS: Supports continuous monitoring of the cardholder data environment and provides evidence that suspicious activity would be detected and addressed.
- SOC 2 (Trust Services Criteria): Helps show customers and auditors that security monitoring and incident response are part of day-to-day operations, not one-off exercises.
- NIS2 and critical infrastructure regulations: Supports expectations for continuous monitoring and operational readiness to detect and manage incidents affecting essential services.
- Customer and supplier security assessments: Provides tangible evidence of monitoring and incident handling, which is often needed to pass due diligence and win contracts.
Which businesses need a SIEM and why
A SIEM becomes necessary when an organisation reaches a scale at which security risks, system complexity, or accountability requirements exceed what individual security tools and manual processes can reasonably handle.
Below are examples of businesses that do and do not yet need a SIEM.
Businesses that need a SIEM
Typical examples: Growing SMEs, regulated organisations, SaaS providers, healthcare and financial services firms, retailers handling customer data, managed service providers, and any business subject to audits, customer security reviews or contractual security requirements.
Most organisations do not proactively adopt a SIEM. More often, the decision follows a cybersecurity audit, customer due diligence process, or a near-miss incident, when it becomes clear the organisation can no longer answer basic security questions quickly and confidently, such as:
- What happened?
- When did it happen?
- Who or what was affected?
This point is typically reached as the organisation scales its existing security tooling and infrastructure. Common signs include:
- Multiple tools (MFA, SSO) and devices (firewalls, routers, switches) from different vendors are generating alerts in isolation
- Security logs are spread across systems with no easy way to search or correlate them
- Incident investigations relying on manual log collection and assumption
- Auditors, regulators or customers expecting clear evidence of monitoring and incident handling for compliance or contract approval
At this stage, a SIEM is less about adding sophistication and more about restoring a minimum viable level of security visibility and control.
It also becomes a commercial requirement, as organisations may lose contracts or fail audits without demonstrable monitoring and incident management capabilities.
Businesses that do not yet require a SIEM
Typical examples: Very small businesses, early-stage startups, sole-trader consultancies, or non-regulated service providers with limited data sensitivity.
A SIEM is unnecessary when an organisation’s environment is still small enough and simple enough to be understood without centralised analysis.
This is typically the case when:
- The environment is limited in scope: For example, organisations with up to 30 users, a small number of endpoints, and a handful of cloud or SaaS applications, with little or no on-premise infrastructure.
- Security tooling is minimal and cohesive: Where most security controls come from a single ecosystem (such as a Microsoft identity and endpoint stack or a single cloud provider’s native security tools), and alerts can be reviewed in one place without needing cross-platform correlation.
- There is little external pressure to evidence security controls: Common in early-stage startups, small professional services firms, or internal teams that are not subject to regulatory audits, formal compliance frameworks, or customer security questionnaires.
- Security incidents are infrequent and straightforward: Issues tend to be limited to common events such as compromised passwords or phishing attempts, and can be understood and resolved using existing logs and built-in dashboards.
In these situations, basic logging, native security dashboards and managed security services may provide adequate coverage. Introducing a SIEM too early can add cost and operational complexity without delivering meaningful additional value.
SIEM implementation and operation
The end-to-end deployment of a SIEM is a lengthy process that typically takes several months. It is a phased programme requiring careful planning, gradual deployment, ongoing adjustment, and ultimately sustained operational management.
This timeframe reflects the need to validate telemetry, integrate relevant context for effective threat detection, and understand normal activity patterns so that alerts are meaningful and reliable.
Below are the key stages of a generalised SIEM implementation and operation:
1. Defining the scope and success criteria of SIEM
Typical timeframe: A few days to weeks
SIEM implementation begins by defining why the organisation is introducing a SIEM and what success explicitly looks like. This stage sets direction and prevents uncontrolled scope growth later.
Organisations typically define:
- Audit or compliance findings identifying gaps in logging, monitoring or incident evidence
- Limited or fragmented visibility across existing security tools
- Slow, manual or inconclusive incident investigations
- Customer, regulatory or contractual requirements to demonstrate monitoring and incident handling
At this stage, the scope is intentionally constrained. Attempting to monitor everything from day one is a well-known cause of SIEM failure, as value comes from prioritisation, not raw data volume.
2. Reviewing existing security and designing SIEM
Typical timeframe: Weeks
With objectives defined, organisations perform a structured review of their existing security tools and the logs they produce to determine how the SIEM can be deployed and operated effectively.
This includes:
- Which systems generate logs
- How logs are stored and accessed
- Where there are gaps or practical constraints
Based on this, decisions are made about deployment model, data collection methods, operating approach, and SIEM platform (e.g. Microsoft or IBM). These choices are driven by operating reality (skills, data location, scale, and budget) rather than ideal architecture.
3. SIEM installation and data onboarding
Typical timeframe: Weeks
Once design decisions are finalised, the SIEM core is deployed and a pilot onboarding phase begins. Initial data sources are deliberately limited to systems that provide the highest security value and context, such as identity platforms, endpoints, critical servers, network devices and key cloud services.
The objective at this stage is reliable, consistent data ingestion, not advanced detection. This phase often surfaces practical issues, including:
- Inconsistent log formats
- Missing or incomplete fields
- Misaligned timestamps
- Excessive noise or unexpected data volumes
Resolving these issues early is critical as poor data quality undermines every later phase. Organisations usually gain basic visibility during this step, but should not expect high-quality alerts yet.
4. Data normalisation, tuning and establishing baseline behaviour
Typical timeframe: Weeks to months
Once data ingestion is stable, the SIEM is prepared for production use. Events are normalised into common structures, irrelevant activity is filtered, and behavioural baselines are established across users, systems and applications so that threats can be judged
This is the most time consuming but critical phase of SIEM implementation. Without proper tuning and baselining:
- Alerts become noisy
- Analysts lose confidence in the platform
- Detection logic produces false positives
Baselines must be built by observing real operational behaviour over time, which is why this phase cannot be rushed.
5. Developing detection, alerting and investigation workflows
Typical timeframe: Weeks
Once data quality and behavioural baselines are established, organisations begin developing detection logic and alerting, starting with a small number of high-value use cases, such as:
- Suspicious login activity or account compromise
- Privileged access outside normal patterns
- Unusual access to sensitive systems or data
Alerts are developed alongside investigation workflows so incidents can be understood, reconstructed and explained, not simply flagged.
Organisations that attempt broad detection too early often overwhelm teams and fail to realise operational value. Successful deployments focus first on accuracy, relevance and explainability, expanding coverage only once trust in detections is established.
At this stage, the SIEM begins delivering early, measurable security and compliance benefits, but it is not yet operating at full maturity.
6. Ongoing SIEM operation and expansion
Typical timeframe: Ongoing
Once the SIEM is in steady state, it enters an ongoing operational phase as the ‘command center’ of the organisation’s cybersecurity. This is where most long-term value is realised, but where most effort is required.
Day-to-day SIEM operation typically includes:
- Alert triage and investigation: Reviewing alerts, validating incidents and escalating where required
- False positive reduction: Adjusting detection logic, thresholds and exclusions based on operational feedback
- Ongoing tuning: Refining parsing, correlation and enrichment as systems and behaviour change
- Content updates: Maintaining detection rules, dashboards and use cases as threats evolve
- Compliance and reporting: Producing operational, executive and compliance reports
Additionally, organisations need to maintain SIEM relevant by expanding its capabilities. This involves:
- Onboarding any additional systems and environments
- Introducing more advanced or behavioural detection as it becomes available
- Integrating response tooling such as SOAR
- Improving compliance and audit reporting workflows
This phase represents continuous operational maturity, not a final endpoint. As environments evolve, risks change and expectations increase, the SIEM must be continuously maintained and refined.
SIEM costs and pricing
While SIEM is arguably the most powerful security tool available, it is also the most expensive to implement and operate.
A relatively simple, cloud-based SIEM deployment for a small organisation can cost £1,000+ per year in license fees, with additional costs for implementation and ongoing management if these services are outsourced. At the other end of the spectrum, a highly customised, enterprise-scale SIEM with 24×7 managed operations can cost £1M or more per year.
Final costs depend on the pricing model selected, the design of the SIEM architecture, and the operating model used. The sections below outline the most common SIEM pricing models and the key cost factors that influence overall spend.
SIEM pricing models
The table below summarises the most common SIEM pricing models and typical service tiers.
| Pricing model | How it works | Typical tier examples (UK) |
|---|---|---|
| Data ingestion–based | Pricing is driven by the volume of log data ingested per day or month; retention may be separate. | Low: ~5–10 GB/day Mid: ~50–100 GB/day High: 500 GB–1 TB+/day |
| User / endpoint / asset-based | Cost is tied to the number of monitored users, endpoints or systems, regardless of log volume. | Low: ~100–250 assets Mid: ~1,000–2,500 assets High: 10,000+ assets |
| Tiered / capacity-based | Predefined bundles cap ingestion, retention or feature sets at each tier. | Low: 25 GB/day + 30-day retention Mid: 100 GB/day + 90-day retention High: 500 GB/day + 1-year retention |
| Platform / bundled subscription | SIEM is included in a wider security platform, unlocked by licence or module tier. | Base: Core logging & alerts Standard: Advanced analytics + compliance Premium: Threat intel, SOAR, extended retention |
| Managed SIEM | Pricing reflects service coverage, data volume and response scope rather than software alone. | Basic: Monitoring only, business hours Enhanced: 24×7 monitoring + triage Full: 24×7 + response & reporting |
SIEM cost factors
SIEM costs are shaped by both initial setup and ongoing operation. Early investment is typically required to onboard and normalise log sources, develop and tune detection use cases, and integrate any response or automation capabilities.
Ongoing costs are primarily driven by:
- Log volume and retention, which determine ingestion, processing, and storage charges
- Architecture and hosting model, including cloud, data transfer, and regional requirements
- Operational effort, covering continuous monitoring, alert triage, investigation, and tuning
- Environmental growth, as new systems and services generate additional telemetry over time
In summary, SIEM should be budgeted as a continuous operational capability rather than a one-time deployment.
SIEM limitations
Despite being powerful, SIEM has significant limitations that organisations should consider before adoption or expansion:
- High cost of ownership: SIEM platforms often require significant ongoing investment in licensing, infrastructure and operational effort, particularly as log volumes grow.
- Operational complexity: Effective SIEM operation requires continuous tuning, maintenance and skilled analysts, which many organisations underestimate.
- Alert noise and false positives: Without careful tuning, SIEMs can generate large volumes of low-value alerts, reducing analyst efficiency and increasing the risk of missed incidents.
- Limited context by default: SIEMs typically rely on log data alone and may lack the business, identity or asset context needed for accurate prioritisation without additional integrations.
- Slow time to value: Deploying and optimising a SIEM often takes months before meaningful detection and response capability is achieved.
- Scalability challenges: As environments grow, ingestion, storage and query performance can degrade or become prohibitively expensive.
- Reactive by design: Traditional SIEMs focus on detecting known patterns and historical activity, rather than proactively identifying novel or emerging threats.
- Dependency on data quality: SIEM effectiveness is directly tied to the quality, consistency and completeness of ingested logs.
- Limited native response capability: Many SIEM platforms provide alerting only, requiring additional SOAR tooling or manual processes for response.
- Skills shortage: Skilled SIEM engineers and analysts are difficult to recruit and retain, leading to increased reliance on managed services.

