Role-Based Access Control (RBAC) Explained
Role-Based Access Control (RBAC) is an authorisation management model that allows organisations to group users and applications into roles with standardised permissions.
It allows security teams to stay on top of user privileges, and is especially useful when there are a dozen or more identities actively using a system.
This guide explains how RBAC works in practice, where fits within within a cybersecurity strategy, how it supports joiner–mover–leaver (JML) processes, and the implementation pitfalls that commonly cause RBAC programmes to fail.
Contents
- What is Role-Based Access Control (RBAC)?
- How role-based access control works
- Why RBAC is important for cybersecurity
What is Role-Based Access Control (RBAC)?
Role-Based Access Control (RBAC) is an authorisation management model that assigns user permissions, such as “read-only” or “write”, by grouping them into roles, rather than granting permissions on a case-by-case basis.
It facilitates the management of large numbers of users and application permissions, allowing administrators to do so consistently and efficiently across the organisation’s digital estate.
Users may be human employees, contractors or guests, or non-human identities such as virtual machines or service accounts connecting via APIs. Equally, permissions may relate to anything from access to local storage and on-premises services to cloud applications.
The RBAC model is typically implemented by administrators through an Identity and Access Management (IAM) platform, such as Microsoft Entra ID or Okta.
Roles may be used to segment access by business department, such as “Finance” or “Legal”, by job function, such as “Account Manager” or “Executive”, or to restrict permissions to specific groups such as “Network Admins”.
For RBAC to play an effective role in cybersecurity, it must be implemented with least privilege in mind, meaning it grants the minimum permissions necessary so that, if a user account is compromised, the potential impact remains restricted.
How role-based access control works
RBAC is the permissions management and enforcement layer that operates only after an identity has gained trusted access (authentication) to a system.
RBAC determines what each authenticated identity can and cannot do based on its assigned roles, whether that involves accessing a specific server or editing files on it.
Regular review over time keeps the system aligned with changes across the organisation’s structure and technologies.
The following is a detailed four-step description of how this works in practice:
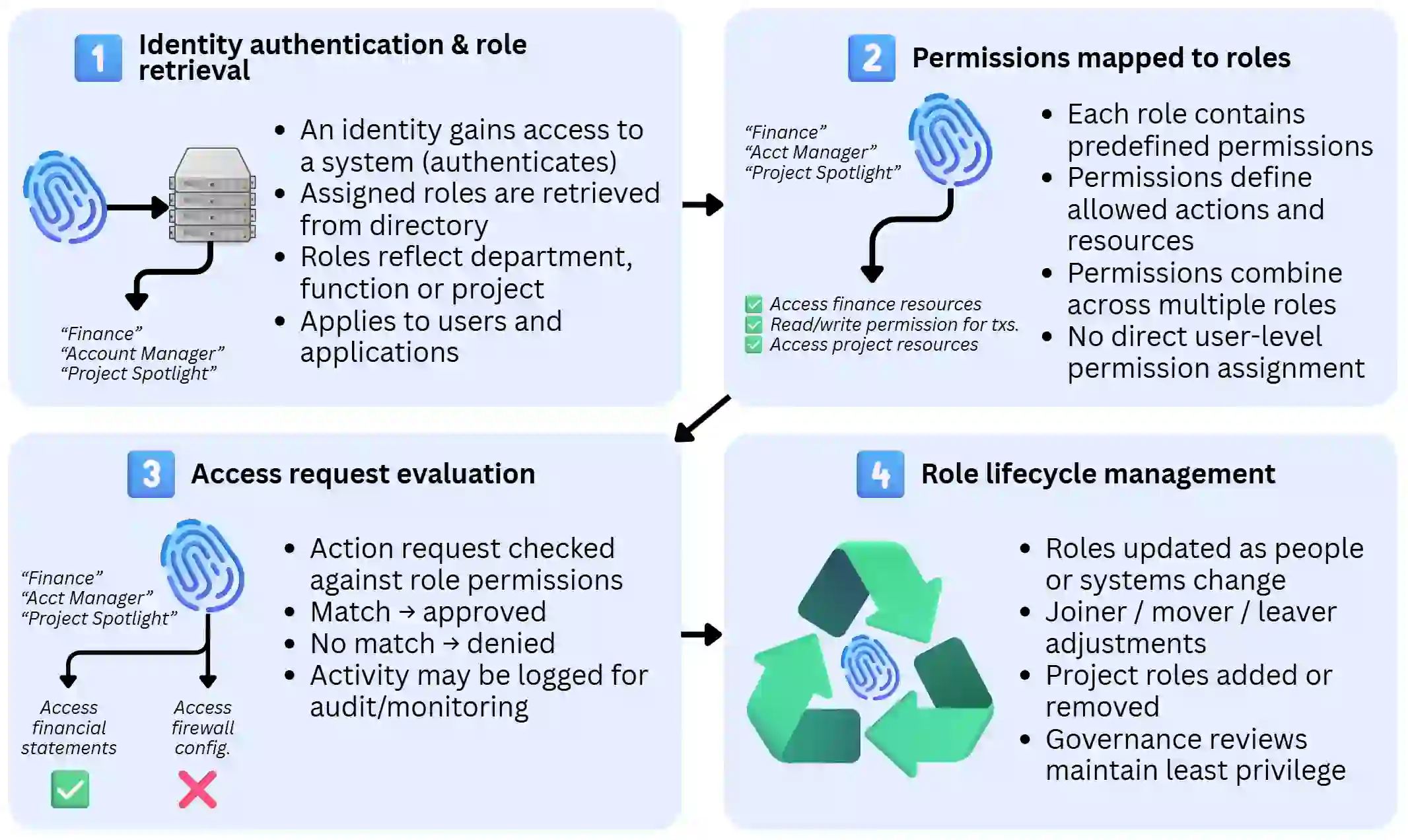
1. An identity is authenticated and its roles retrieved
Access to a system begins with identity authentication, meaning the user or application provides the necessary credentials to prove it can be trusted.
In an RBAC-protected system, this authentication triggers the retrieval of any roles assigned to the identity, which are stored in the system’s identity directory.
For example, user “J.Doe” joins an enterprise and is assigned to three role groups:
- “Finance”, meaning he is part of the finance department.
- “Account Manager”, signalling its specific job role within that department.
- “Project Spotlight”, indicating a specific ad-hoc, multi-disciplinary project.
2. Permissions are derived from assigned roles
Each role has an attached, predefined set of permissions representing what it is allowed to access or perform. For instance:
- “Finance” grants read access to local storage and finance cloud platforms.
- “Account Manager” allows the approval or rejection of financial transactions for a specific account.
- “Project Spotlight” grants read or write access to a project-specific database, independent of the other roles.
If “J.Doe” were an API rather than a human user, the same permissions model would apply if it were placed within the same roles.
3. Access requests are evaluated against permissions
Whenever an identity makes an action request, the RBAC system compares the request against the permissions attached to its roles.
In the case of user J.Doe, the following would occur:
- Approved: A request to download data from the Project Spotlight database would be allowed because it is included within the role’s permissions.
- Denied: A request to configure DNS, antivirus or VPN settings would be rejected because J.Doe does not have an IT administrator role.
- Approved: A request to approve a payment for his client would go through because J.Doe is both part of the Finance department and the manager for that client account.
Permission approvals and rejections may be stored temporarily in security logs for forensic purposes, in case the organisation suffers from a cybersecurity incidents. In large companies, this is usually centralised in a SIEM.
4. Permission management and lifecycle control
An RBAC system must reflect organisational and system changes, whether they relate to headcount, role transitions, project lifecycles, new APIs, cloud applications, or virtual environments.
Continuing the J.Doe example:
- If Project Spotlight (or J.Doe’s involvement) ends, the “Project Spotlight” role can be removed from J.Doe, automatically revoking his access to all associated resources.
- If J.Doe moves from Finance to Accounting, IT reassigns him to the “Accounting” role. His permissions change immediately without individual manual adjustments.
- If J.Doe is promoted from “Account Manager” to “Executive”, his previous role can be replaced with a managerial role carrying broader approval permissions.
- If the Finance team begins using a CRM platform, its API permissions can be attached to the “Finance” role, automatically extending access to J.Doe and others in that role.
Why RBAC is important for cybersecurity
RBAC is a critical cybersecurity control because it governs the permissions granted to trusted identities that have access to a system. Authentication confirms that an identity is valid, but RBAC determines the scope of its actions.
Its importance can be understood in three core areas:
Limits the impact of compromised accounts
Most security breaches involve the misuse of legitimate credentials stolen through phishing, email compromise, or other attacks.
Once an attacker gains access to a valid account, RBAC determines how far they can move within the system.
When roles are designed around least-privilege principles, each identity is restricted to only the resources and actions necessary for its function.
For example, a finance assistant may be able to view invoices but not modify payment details. An API integration may have read-only access rather than full administrative rights.
If one of these identities is compromised, the attacker inherits only the permissions attached to that role. Sensitive systems, approval rights and administrative controls remain inaccessible.
RBAC therefore reduces the blast radius of an incident by preventing a single compromised account from escalating into a wider breach.
Prevents excessive or outdated permissions
Without structured role assignment, administrators are forced to grant permissions manually, which makes review and management time-consuming and complex.
Without RBAC, permissions tend to accumulate on individual accounts, creating over-access that is difficult to detect and justify, or extreme restrictions that make the user experience difficult.
These two common problems are known as:
- Over-permissioning: Identities gradually gain access beyond what is required through ad hoc permissions, exceptions, or unstructured role design.
- Privilege creep: A specific type of over-permissioning where employees or APIs retain access from previous roles or projects, due to a lack of structure in the authorisation processes.
RBAC mitigates both risks by tying permissions to defined roles rather than to individuals. When someone changes position, leaves a project, or exits the organisation, their permissions are automatically updated through role reassignment.
This keeps access aligned with current responsibilities and reduces the likelihood of dormant or excessive privileges remaining.
Enforces separation of duties and internal controls
RBAC also supports governance controls by preventing the assignment of conflicting permissions to the same identity.
For example, a user may be allowed to create payments but not approve them, or to develop code but not deploy it to production. These separation-of-duties controls are fundamental to fraud prevention and regulatory compliance.
Because permissions are structured through roles rather than granted individually, conflicts are easier to detect and prevent at the design level.
This adds a layer of internal control that complements authentication and network security measures, reducing both insider risk and operational misuse.
RBAC and compliance requirements
RBAC supports several core compliance principles that appear across a wide range of UK standards and regulations.
GDPR
Under the UK General Data Protection Regulation, organisations must implement appropriate technical and organisational measures to protect personal data (Article 32).
RBAC supports GDPR compliance specifically by:
- Limiting access according to role requirements, ensuring personal data aligns with business needs.
- Protecting integrity and confidentiality by reducing excessive access and limiting exposure if credentials are compromised.
- Supporting accountability by structuring access around defined roles, which can be reviewed and audited alongside logging systems.
ISO 27001
The ISO 27001 standard requires access to be controlled in accordance with business and security requirements.
RBAC supports this by:
- Formalising access policy through documented role definitions
- Enforcing least privilege by grouping permissions by responsibility
- Improving review quality, as managers validate role membership rather than individual permissions
- Supporting segregation of duties through structured role separation
Industry-specific regulatory frameworks
Many sector frameworks reinforce access control and least privilege principles, including:
- Financial Conduct Authority (FCA) Handbook
- NHS Data Security and Protection Toolkit
- PCI DSS (For card payments)
Common expectations across these frameworks include those features that RBAC provides, such as:
- Access restricted to authorised roles
- Controlled and reviewed privileged access
- Permissions aligned to current responsibilities
- Prompt removal of leaver access
How RBAC fits within a wider cybersecurity strategy
RBAC is important, but it is ultimately a single component of any cybersecurity strategy. It primarily sits within the discipline of identity security, but also complements network, endpoint and monitoring controls elsewhere in the security architecture.
How RBAC fits into identity security and IAM
Identity security is the overarching discipline concerned with how users, applications and systems are authenticated, authorised, monitored and removed across an organisation.
Within this discipline, Identity and Access Management (IAM) provides the core infrastructure. IAM platforms such as Microsoft Entra ID and Google Cloud IAM act as the technological engine for identity security, maintaining directories, issuing tokens and enabling centralised access control.
RBAC operates at the authorisation layer within IAM. It is typically implemented as a configuration component of the IAM platform, where administrators define roles, attach permissions and assign them to identities from a centralised interface.
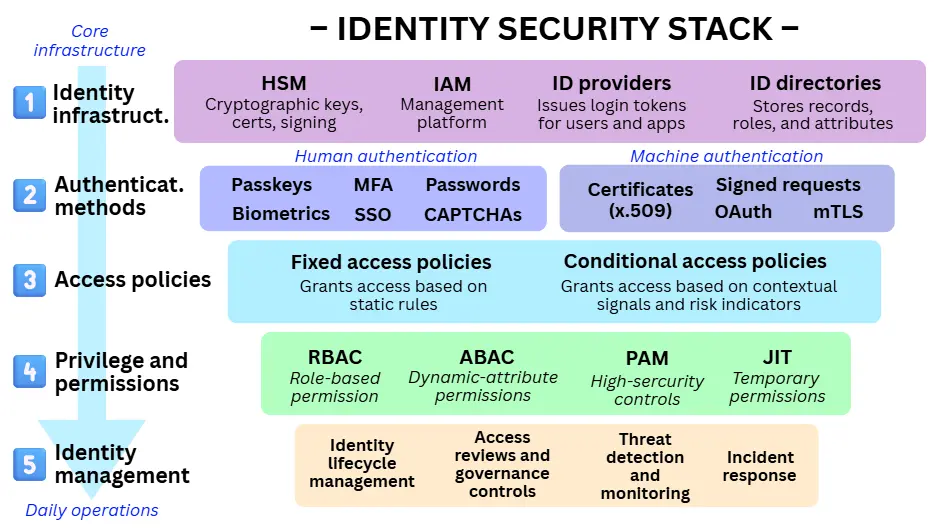
RBAC does not replace authentication controls such as Multi-Factor Authentication (MFA), Single Sign-On (SSO) or conditional access policies.
It operates after authentication, determining what a verified identity is permitted to do. If authentication controls are bypassed, RBAC can still limit the blast radius by restricting the scope of that identity’s permissions.
RBAC also works alongside other authorisation and privilege controls within the same layer:
- ABAC (attribute-based access control) enables dynamic, context-based permission decisions.
- Privileged Access Management (PAM) strengthens control over high-risk administrative roles.
- Just-in-Time (JIT) access reduces standing privilege by making sensitive permissions temporary.
RBAC is closely tied to identity lifecycle management. Joiner-mover-leaver (JML) processes, periodic access reviews and governance controls rely on structured role assignment to ensure permissions remain aligned with organisational change.
How RBAC complements other cybersecurity controls
RBAC is a powerful controller of identities, but even the best setups have some vulnerabilities. If an attacker compromises an identity that legitimately holds broad administrative permissions, RBAC will enforce those permissions as configured.
For this reason, RBAC operates within a layered security model alongside other technical controls that constrain movement at the wire level and inspect traffic even when it comes from an authorised user. These include:
- Network segmentation (such as VLANs): Restrict communication between systems and environments. Even if an identity has application-level permissions, segmentation can limit lateral movement across infrastructure.
- Firewalls and Web Application Firewalls (WAFs): Inspect and filter traffic, blocking malicious payloads or abnormal requests, including those originating from authenticated users.
- Endpoint Detection and Response (EDR): Monitors behaviour on user devices and cloud workloads. It can detect suspicious privilege use, abnormal access patterns or data exfiltration attempts, even where actions fall within assigned permissions.
- Security Information and Event Management (SIEM): These platforms aggregate logs from IAM, RBAC, network and endpoint systems. By correlating activity across layers, SIEM tools help identify complex attacks and provide longer-term audit visibility.
How is RBAC implemented in businesses?
RBAC is typically implemented as part of establishing an organisation’s identity security framework. It follows the rollout of authentication controls (e.g., passkeys, conditional access, MFA), once systems and internal permissions are ready to be structured properly.
The process is practical and structured, beginning with planning and role design, moving into configuration, and concluding with lifecycle integration and ongoing governance.
Below is a general step-by-step approach.
1. Define scope and ownership
Organisations begin by deciding where RBAC will apply and who is responsible for managing it. This includes:
- Identifying which systems are in scope first, such as Microsoft 365, finance software, HR platforms or CRM systems.
- Deciding whether roles will be managed centrally through an IAM platform such as Microsoft Entra ID or Google Cloud IAM, or inside each application.
- Assigning a clear owner for role definitions and approvals, usually a senior IT administrator.
2. Design roles based on real job functions
Roles should reflect the organisation’s size, operational complexity and security requirements. They may range from simple distinctions such as “admin” and “non-admin” to hierarchical or constrained models that incorporate categories such as seniority, department, or project.
In practice, organisations typically:
- Create separate roles where access to sensitive or personal data is required
- Keep administrative or high-risk roles separate from normal user roles
3. Decide where roles will be enforced
RBAC can be enforced at different layers depending on the system architecture. While most organisations aim for centralised management through an IAM platform, roles may exist at multiple levels.
The main options are (going from decentralised to centralised):
Application-level RBAC
Roles are defined inside a specific system, such as a CRM, finance tool or HR platform. This is common when the software has built-in roles like “Manager” or “Editor,” or when in-house applications require roles to be coded directly. It is often necessary when permissions are highly specific to that application.
Platform-level RBAC
Roles govern access across a broader technical environment, such as Microsoft Azure or Google Cloud Platform. This model is typically used by IT and DevOps teams to manage infrastructure, subscriptions, storage, or virtual machines.
IAM-level RBAC
Roles are created centrally within an identity platform (such as Microsoft Entra ID, Okta or Google Cloud IAM) and linked to multiple systems. This approach supports consistent joiner–mover–leaver processes and easier governance.
In general, centralised RBAC is easier to manage and review, although technical constraints often require a combination of approaches.
4. Configure roles and link them to permissions
Once roles are defined conceptually, they must be configured within the systems that enforce access.
In many environments, roles are implemented as “groups” or role objects (containers for identities), with permissions attached at the group level.
The practical steps are:
- Create a group in the IAM platform that represents each defined role (e.g., “Finance Analyst”).
- Adding relevant users to the group and validating membership with business owners.
- Linking that group to the required permissions within each relevant system, such as read access to finance reports or approval rights in an accounting platform.
From that point onwards, access flows from group membership. Removing a user from the group automatically removes their associated permissions.
5. Run a pilot and validate the role model
RBAC can disrupt user experience or introduce risk if misconfigured, so controlled testing is essential.
Organisations often begin with one department or high-value system and pilot the new role structure.
Typical validation steps include:
- Comparing existing permissions with the proposed RBAC model.
- Confirming users can perform their duties without unnecessary access.
- Identifying missing permissions, excessive access or workflow gaps.
- Refining role definitions as required.
A pilot reveals real-world edge cases that may not be apparent during planning. Once validated, the model can be expanded with greater confidence.
6. Integrate RBAC with Joiner–Mover–Leaver (JML) processes
RBAC only delivers long-term value when it is embedded into the organisation’s Joiner–Mover–Leaver (JML) processes, the formal way identities are created, changed and removed over time.
Because RBAC ties permissions to roles rather than individuals, JML becomes a matter of role management rather than manual permission adjustment.
In practice, this means:
- Joiners: Receive baseline access through predefined role assignment aligned to their job function.
- Movers: Remove previous roles before assigning new ones to prevent privilege creep.
- Leavers: Lose access immediately when their identity is disabled or deleted, as all role-based permissions are withdrawn.
In mature environments, IAM platforms such as Microsoft Entra ID or Okta integrate with HR systems so that employment status changes automatically trigger role assignment or removal rules. However, governance oversight is still required to ensure roles remain accurate and appropriately scoped.
Embedding RBAC into JML processes ensures that access reflects current responsibilities rather than historical ones.
7. Establish ongoing review and governance
RBAC requires continuous review to remain accurate and compliant. Best practices include:
- Running periodic, scheduled reviews of role membership, especially for high-risk or privileged roles
- Reviewing role definitions when systems, processes or regulations change
- Applying change control (have a clear approval process, amending permissions to a role).
- Removing any unused or outdated roles and determining why they are still there.
Most IAM platforms support access reviews, but the responsibility for approving them typically sits with business managers, not IT.
RBAC limitations and challenges
RBAC is widely adopted because it introduces structure and clarity to authorisation control. However, it is not a complete identity security solution, and it has inherent structural and operational limitations that must be addressed through complementary controls and strong governance.
Its main limitations fall into three areas:
RBAC is static by design
RBAC grants permissions through predefined roles. Once a role is assigned, access remains unchanged until it is manually modified.
This model does not automatically consider contextual or real-time factors such as device security, unusual login behaviour or session risk. As a result:
- Access does not adapt dynamically to changing conditions.
- Temporary or short-term access requires explicit management.
- If credentials are compromised, the attacker inherits the full permission set attached to that role.
In environments adopting zero trust principles, organisations often complement RBAC with additional authorisation models:
- Attribute-based access control (ABAC) introduces contextual decision-making based on factors such as device compliance, location or time of access.
- Privileged Access Management (PAM) applies stricter controls to high-risk roles, including time-limited access, approval workflows and activity monitoring.
These controls do not replace RBAC but strengthen areas where static role assignment is insufficient.
RBAC becomes complex as organisations scale
RBAC performs best when job functions are stable and clearly defined. As organisations grow, introduce matrix structures or adopt highly granular systems, complexity increases.
Common scaling challenges include:
- Role explosion: A growing number of narrowly defined roles created to reflect small variations in responsibility.
- Role sprawl: Overlapping or slightly differentiated roles accumulating over time.
- Administrative overhead: Increasing effort required to review, maintain and validate role definitions and memberships.
Without careful design, the model can become difficult to manage and harder to audit.
RBAC depends heavily on governance discipline
RBAC is structurally simple. Permissions are grouped into roles, and roles are assigned to identities. Its effectiveness, however, depends on consistent governance.
If roles are poorly designed, rarely reviewed or loosely controlled, the model gradually drifts away from least-privilege principles. Over time, permissions expand beyond what is genuinely required, and the clarity that RBAC was meant to provide is lost.
Without regular review, role definitions can become outdated, exceptions accumulate, and access no longer reflects real business responsibilities. This weakens both security posture and audit defensibility.
These risks arise from weak governance rather than flaws in the RBAC model itself.
Role-based access control (RBAC) FAQs
Our business broadband experts answer frequently asked questions regarding RBAC:
When should businesses review or redesign their RBAC model?
RBAC should be reviewed regularly, on a scheduled and predictable basis, as part of ongoing governance. Periodic reviews help ensure roles remain aligned with real responsibilities and continue to reflect least-privilege principles as the organisation evolves.
That said, a targeted reassessment is warranted when significant change occurs, such as rapid headcount growth, restructures, mergers, repeated access exceptions, audit findings, security incidents, or major system changes, including cloud migration or new SaaS adoption.
What is the difference between Core, Hierarchical and Constrained RBAC?
RBAC can be implemented with increasing levels of structure depending on organisational size and security needs. There are three models:
- Core RBAC: The basic form where users are assigned to roles, and roles are assigned permissions. There is no inheritance or additional restrictions.
- Hierarchical RBAC: Adds role inheritance, where senior roles automatically inherit the permissions of junior roles. This reduces duplication and supports larger organisational structures.
- Constrained RBAC: Introduces governance controls, such as separation of duties. For example, a user may be prevented from both creating and approving payments, reducing fraud risk and supporting compliance.
Most modern IAM platforms combine these capabilities as needed.

