Border Gateway Protocol (BGP): How Internet routing works
Border Gateway Protocol (BGP) is the core routing system of the internet, directing traffic across thousands of independent networks without any central control.
Every website visit, cloud request, or VoIP call relies on BGP to continuously map and update the best path between networks.
This guide explains what BGP is, how it works, and what it means for business connectivity.
Contents:
- What is the Border Gateway Protocol?
- How Border Gateway Protocol works
- BGP multi-homing: Enterprise-grade redundancy solution
- BGP security risks and protections
What is the Border Gateway Protocol?
Border Gateway Protocol (BGP) is the routing protocol responsible for directing traffic between the tens of thousands of independent networks that make up the internet.
In BGP speak, these networks are called Autonomous Systems (AS). They are independently operated by last-mile internet service providers (ISPs), cloud providers, telecom companies, and large enterprises, without a central authority coordinating routing across them.
BGP interconnects this decentralised patchwork of networks by sharing real-time routing information across a network-to-network peering system.
Network edge routers form the backbone of this global peer-to-peer system, each maintaining and continuously sharing the real-time status of internet paths and routing preferences with the peer routers of their neighbouring AS.
When a business requests to connect with a resource or service in a separate network (e.g., accessing a website hosted in AWS), the ISP’s routing infrastructure uses BGP to determine the best path.
Once the route is determined, a TCP (Transmission Control Protocol)/IP connection can be established between the business and the service to enable the transfer of data, as shown in the diagram below.
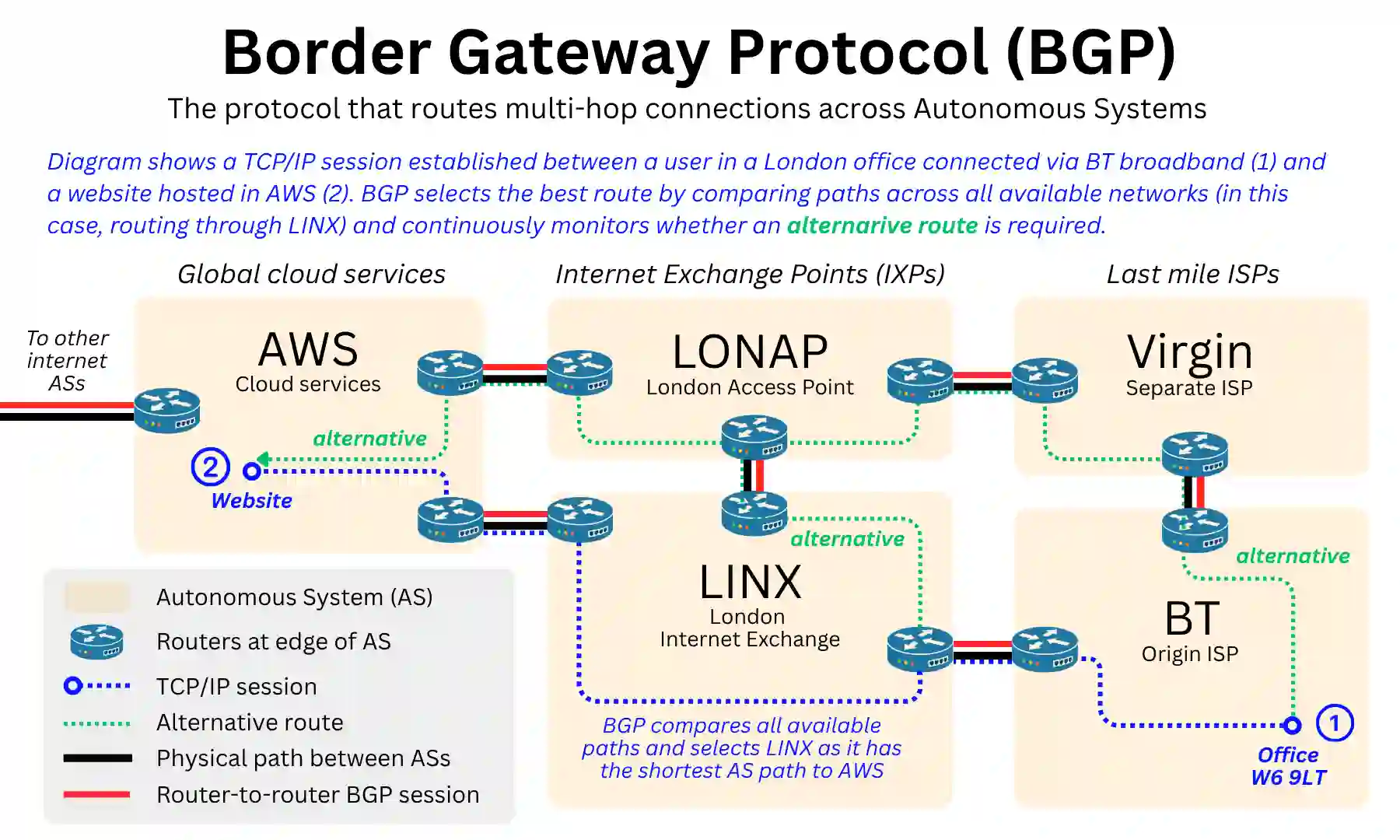
To see how BGP fits alongside the other systems running the internet, consider a device in a London office loading a webpage hosted on an AWS server.
- Access request: An employee types “https://www.aquaswitch.co.uk” into their browser.
- Domain Name Service (DNS): Resolves the website’s domain name into an IP address. In this case, hosted on AWS in London.
- Border Gateway Protocol (BGP): Determines the end-to-end path between the office and AWS, hopping across every network that sits between the ingress and egress routers. In this example, routing through BT, across the LINX internet exchange, and into AWS.
- TCP/IP session established: The browser and server open a communication channel.
- TCP: Breaks the data into packets, sends them along the path, and ensures they arrive completely and in order.
Each system operates at a different layer, handling a distinct part of the internet communication process.
BGP’s role is to determine the routes that make connections across the internet possible, even for two geographically close points. If the route becomes unavailable, for example, due to a broadband infrastructure issue, BGP can re-route across alternative paths.
How Border Gateway Protocol works
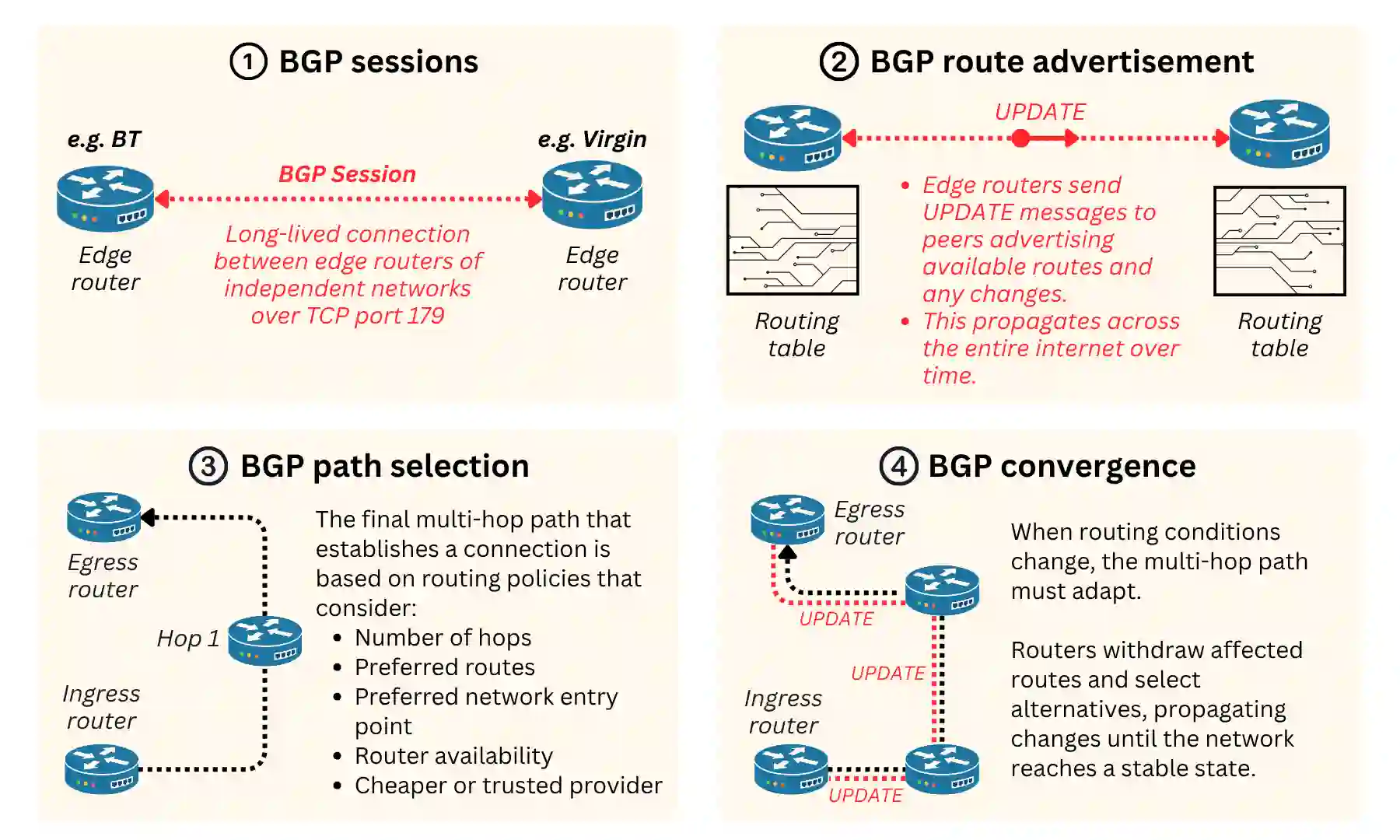
BGP relies on four key mechanisms to achieve autonomous, decentralised internet routing between Autonomous Systems (ASs):
- BGP sessions: Long-lived, router-to-router communication of live routing data.
- BGP route advertisement: Messaging of available routes through chains of BGP sessions.
- BGP route: The established multi-hop route for internet communication sessions.
- BGP convergence: Communication of route changes through BGP route advertisement.
Additionally, BGP relies on a separate, fifth mechanism called Internal BGP (iBGP) to determine routing within each AS.
Below, we explain each of these five mechanisms in detail and how they work together to achieve BGP routing:
BGP sessions: The foundation for internet routing
Reaching any service over the internet requires a chain of BGP sessions between routers at the boundaries of Autonomous Systems, stretching from the router at the edge of the user’s local network all the way to the target network.
A BGP session is a persistent, long-lived communication channel between routers in directly connected, adjacent networks.
Through it, routers continuously share routing information (i.e., the paths available, their current status, and any changes as they happen).
These sessions are a core part of any router’s functionality and are pre-configured by the network operators on either side of the connection, typically because they have a physical link and a commercial agreement to exchange routing information.
For example, a large network operator like BT will have hundreds of adjacent networks (i.e., other internet service providers, transit providers, and major platforms like AWS or Google) and maintains active BGP sessions with all of them.
When a device requests to connect to a service, the router at the edge of its local area network will:
- Read the destination IP address from the data packet.
- Look up that destination in its routing table, which is built and continuously updated from the information exchanged across its active BGP sessions.
- Identify the best path through the AS (the sequence of BGP sessions between the Autonomous Systems that the data must traverse to reach its destination): Origin AS > AS1 > AS2 > AS3 > Target AS)
Through this chain of BGP session pairs, the router is capable of mapping the AS path that data packets would need to take to start the TCP/IP session between the ingress and egress routers.
This is required to exchange data between the user’s device and the target service, whether that is loading a website, making a VoIP call, or uploading files to the cloud.
Route advertisement: Real-time route status updates
The end-to-end chain of BGP sessions (the AS path) depends on the consistency of route advertisements between them.
A route advertisement is the mechanism through which a network advertises its routes to its direct BGP neighbours through the BGP session.
When a router advertises a route, it is telling its peer: “traffic destined for these IP addresses can reach its destination through me.” This is communicated through a BGP UPDATE message, which contains:
- The network prefix: The group of IP addresses being advertised.
- The AS path: The sequence of Autonomous Systems the advertisement has travelled through so far.
- A set of path attributes: This includes the next-hop router address.
- Any operator-configured preferences: These influence how the receiving router handles it.
When a network like AWS wants to be reachable from anywhere on the internet, it advertises its network prefixes to all of its direct BGP neighbours.
Those neighbours add the information to their routing tables and pass the advertisement along to their own neighbours, propagating outward across the internet’s BGP sessions automatically.
Each hop adds its own AS number (ASN), a unique identifier assigned to every Autonomous System, to the AS path as it goes.
The result is the AS path, a complete record of the route the advertisement has travelled (e.g. AS1 > AS34 > AS67 > AS123 > AS777).
When a new service comes online, or when an existing one changes its network prefixes (IP addresses), that information ripples outward across the chain in the same way.
Routers do not simply accept every advertisement they receive. Each one evaluates incoming routes against its own configured policies: filtering, prioritising, or rejecting certain advertisements based on commercial agreements, performance requirements, or security rules set by the AS operator.
The result is a routing table that reflects not just what is reachable, but what that particular network has decided is the best and most trusted way to reach it.
BGP path selection: Choosing the end-to-end AS path
With routing tables built from continuous route advertisements, every router along the AS path holds information about multiple possible routes to the same destination.
BGP path selection is the process by which a router decides which of those routes to use. Each router evaluates available routes against a set of path attributes in a strict order of priority, discarding less preferred options at each step until one route remains.
The key attributes considered include:
- AS path length: The number of Autonomous Systems the route passes through. Shorter is generally preferred.
- Local preference: An operator-configured value that allows a network to favour certain routes over others, regardless of path length.
- MED (Multi-Exit Discriminator): A value advertised by a neighbouring AS to suggest a preferred entry point into their network.
- Next-hop reachability: The next router in the path must itself be reachable; the route is discarded.
BGP does not simply choose the shortest or fastest path; it follows policy. ISPs can actively influence which routes traffic takes, prioritising a cheaper transit provider over a faster one, or routing traffic away from a congested network.
BGP path selection is a commercial and operational decision as much as a technical one.
Note that BGP path selection is not affected when using SD-WAN routing optimisation, as this operates at the network layer, choosing from available enterprise WAN paths within the paths selected by the BGP. See our detailed SD-WAN explainer to understand the difference.
BGP convergence: What happens when routes change
For the internet to remain operational 24/7, it needs to be highly adaptable. Routing needs to adapt to both scheduled (e.g., new installations, maintenance) and unscheduled (e.g., logical and physical failure of links) changes in infrastructure.
When a failure is detected within the routing domain of an edge router, a BGP convergence process is triggered, where the router sends a BGP UPDATE message to all its peers.
The message contains the affected prefix (i.e., group of IP addresses) so the peer can remove it from its routing tables, select an alternative route if one exists, and propagate the withdrawal further across the network.
This UPDATE message ripples outward across the internet until every router adjusts, re-routing any live TCP/IP connections running over it. The time it takes for a network to reach a consistent state after a change is known as convergence time.
During this window, routing is unstable. Some routers may still be sending traffic along a disrupted path that others have already withdrawn, leading to packet loss, increased latency, or brief outages.
Convergence time is influenced by the size of the network, the number of BGP sessions affected, and the rate at which UPDATE messages propagate across peers.
In large, complex networks, convergence can take anywhere from a few seconds to minutes, explaining why internet disruptions rarely recover the moment an underlying issue is fixed.
iBGP: Routing within networks
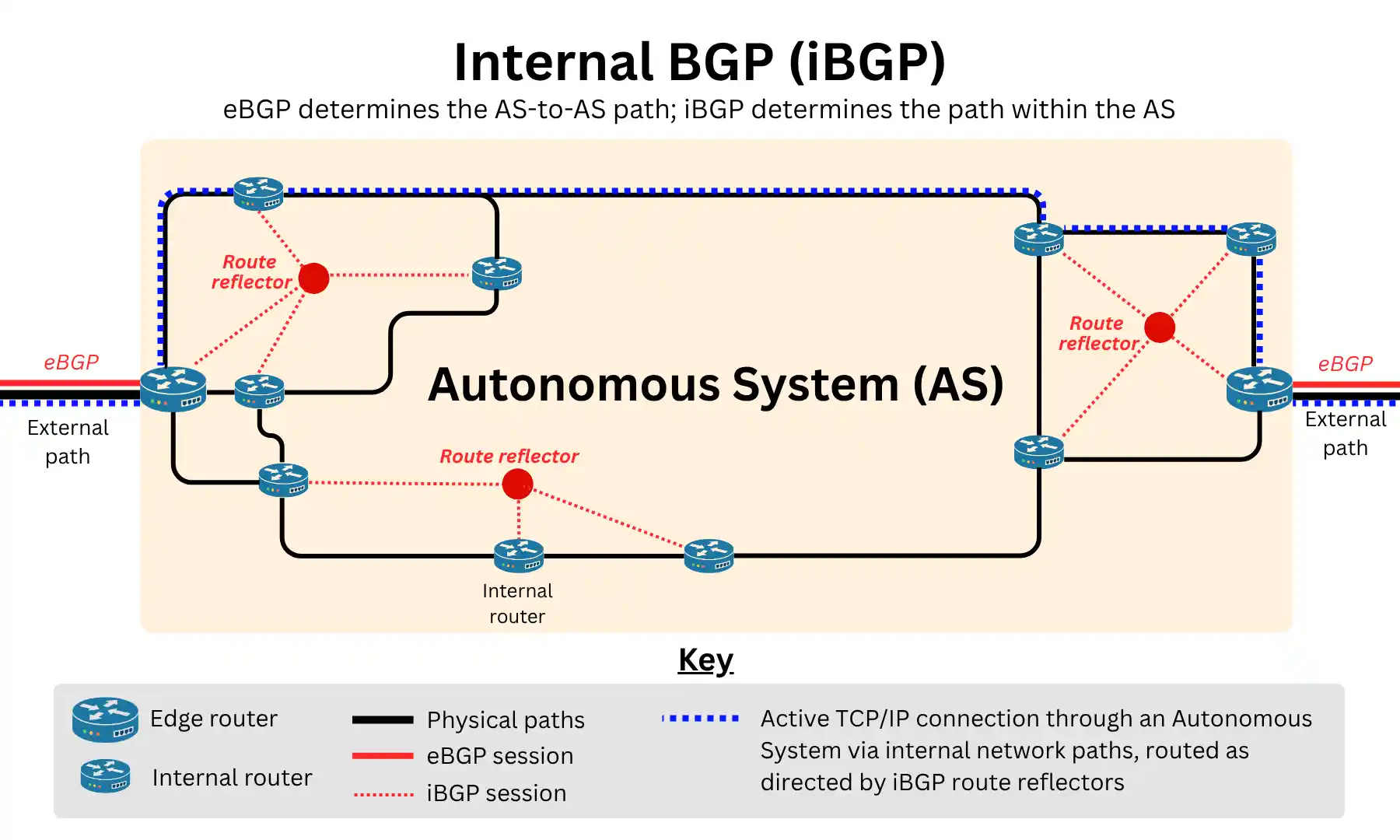
The BGP sessions discussed so far are all forms of External BGP (eBGP), which interconnects Autonomous Systems (AS) to form the global patchwork of the public internet.
But these networks have vast internal infrastructures consisting of hundreds to thousands of routers. Once traffic arrives at their edge, Internal BGP (iBGP) takes over, carrying it across that internal infrastructure to the egress router, where it is forwarded to the next AS.
iBGP ensures that routing information learned at the edge is consistently shared across every single internal router within the network.
However, iBGP routers do not re-advertise routes learned from one peer to another like in eBGP, because doing so risks creating routing loops, where traffic circulates indefinitely between routers rather than reaching its destination.
To solve this, iBGP utilises route reflectors, designated routers that act as a central distribution point for routing information.
Rather than every internal router maintaining a session with every other router, each only needs a session with its route reflector, which then distributes routing information across the AS on its behalf.
BGP multi-homing: Enterprise-grade redundancy solution
BGP multi-homing is an advanced connectivity service that allows an organisation to connect to multiple ISPs simultaneously and participate directly in internet routing decisions.
It is used by organisations running critical infrastructure such as data centres, financial institutions, and large media companies like the BBC, where router or WAN-level redundancy alone is insufficient.
Why BGP multi-homing is necessary over Dual-WAN routing
Most organisations implement redundancy at the router level through a Dual-WAN router: Two connections from two separate ISPs, with automatic failover if one goes down. This is sufficient to maintain general internet and cloud access.
The limitation appears when an organisation needs to host services on-premises. Each ISP assigns its own IP addresses (regardless of whether they are dynamic IPs or static IPs), meaning inbound traffic to mail servers, VPNs or customer-facing applications is tied to whichever ISP issued those IPs.
If that ISP fails, inbound connectivity is lost regardless of whether a second connection is active.
BGP multi-homing solves this by giving the organisation its own Provider Independent IP address space, advertised through both ISPs simultaneously.
Inbound traffic can arrive via either connection, and if one ISP fails, BGP convergence automatically re-routes everything through the surviving link, with no manual intervention and no change in IP address.
How BGP multi-homing works
The organisation obtains its own Autonomous System Number (ASN) and a Provider Independent (PI) IP address block. It then establishes BGP peering sessions with two or more ISPs and configures its edge router to advertise its IP prefixes through each ISP simultaneously.
This means the wider internet sees those IP addresses as reachable via multiple paths. If one ISP fails, BGP convergence automatically re-routes all traffic through the surviving connection, with no change in IP address and no manual intervention required.
Outbound traffic can be distributed across both links using routing policy attributes such as local preference and AS-path prepending. Inbound traffic distribution can also be influenced using these attributes, though with less precision than outbound.
Because BGP peering requires a direct session between the organisation’s edge router and each ISP’s router, standard broadband products are not suitable. This type of connectivity requires enterprise-grade circuits such as leased lines or MPLS.
BGP multi-homing implementation options
BGP multi-homing can be deployed in three major ways depending on an organisation’s size, technical capability, and scope for managing infrastructure.
Self-managed
The organisation manages BGP peering, routing policies, and failover behaviour entirely in-house using enterprise routing hardware. This offers the highest level of control but demands dedicated network engineering capability. Best suited to data centres, financial institutions, and large enterprises.
Managed service
The organisation retains its ASN and IP space, but a specialist provider such as BT Wholesale or Virgin Media Business handles peering configuration, route management, and ongoing maintenance. This makes BGP multi-homing accessible without in-house expertise, at the cost of some direct control.
Cloud-delivered
Providers such as Cloudflare Magic Transit absorb the organisation’s IP space and advertise it globally via BGP, adding DDoS protection in the process. Major cloud platforms, including AWS, Azure, and Google Cloud also support native BGP sessions for organisations connecting private infrastructure to public cloud environments.
BGP security risks and protections
BGP operates at the infrastructure level of the internet, meaning security at this layer is the responsibility of whoever operates the Autonomous System: The ISP, cloud provider, or, in the case of BGP multi-homing, the organisation itself or its managed service provider.
For most businesses, especially SMEs, BGP security is not something that needs to be actively managed, but it is worth understanding that BGP carries some inherent risks, especially because it was built without security in mind.
The main security risks are:
- BGP hijacking: A malicious or misconfigured AS advertises someone else’s IP prefixes, redirecting their traffic. High-profile incidents have affected major platforms and financial institutions.
- Route leaks: An AS accidentally propagates routing information it should not, causing traffic to flow through unintended networks and potentially degrading performance or exposing data.
- Lack of built-in authentication: BGP was designed for trust between networks, not security. Without additional controls such as RPKI (Resource Public Key Infrastructure), there is no native mechanism to verify that a route advertisement is legitimate.
- DDoS exposure: Organisations advertising their own IP space via BGP multi-homing become more visible on the internet, potentially increasing their exposure to volumetric attacks.
Border Gateway Protocol (BGP) – FAQs
Our business broadband experts answer the most commonly asked questions about Border Gateway Protocol and how it affects UK businesses.
Does my business need to worry about BGP?
For the vast majority of businesses, especially SMEs, BGP operates invisibly in the background, managed entirely by their business broadband provider.
Unless you are hosting services on-premise that require inbound connectivity or need redundancy beyond what a standard Dual-WAN setup provides, there is nothing to configure or monitor. BGP only becomes a direct concern if you are implementing multi-homing with your own ASN and IP space.
Can BGP be used for internet failover?
Yes, it can be a powerful internet failover by implementing BGP multi-homing with their own ASN and IP space. However, this is a sophisticated and costly solution only suitable for specialised or large organisations.
For most businesses, failover can be handled at the router level or via an SD-WAN solution.
What is the difference between BGP and OSPF?
BGP (which typically refers to eBGP or external BGP) and OSPF are both routing protocols, but they operate at very different scales and serve different purposes.
OSPF (Open Shortest Path First) is an interior gateway protocol, used to manage routing within a single network, typically inside a large enterprise or ISP’s own infrastructure. It builds a complete map of the internal network topology and calculates the shortest path to each destination based on link costs.
eBGP is an exterior gateway protocol, designed to manage routing between separate, independent networks across the internet. This is the form of BGP most people mean when they refer to BGP.
However, large networks also run iBGP (Internal BGP) internally alongside OSPF.
Where OSPF calculates the best internal path based on topology, iBGP distributes the external routing information learned at the network’s edge (via eBGP sessions with neighbouring ASs) consistently across all internal routers.
In practice, a large ISP will typically run all three simultaneously:
- OSPF to route traffic across its own infrastructure
- iBGP to propagate external routing information internally
- eBGP to exchange routing information with the rest of the internet.
Why do major internet outages often involve BGP?
BGP is the protocol that holds the internet together. When a large AS misconfigures a route advertisement or accidentally withdraws a prefix, that change propagates outward across thousands of BGP sessions.
Traffic destined for the affected network suddenly has no valid path and drops. The 2021 Facebook outage is a well-known example, where an internal BGP configuration change caused Facebook’s entire network to disappear from the internet’s routing tables for several hours.
Because BGP convergence takes time, recovery is rarely instantaneous even once the error is corrected.
Does my leased line use BGP?
Yes. A leased line is a dedicated internet connection between a business’s premises and the ISP’s network, and BGP is the protocol the broadband provider uses to route traffic from that connection across the internet.
See our guide to leased line business broadband to understand its mechanics in detail.
On enterprise leased line products, it is also possible to establish a BGP peering session directly with the ISP, which is a prerequisite for BGP multi-homing.
Do I need my own AS number to use BGP?
Not for standard internet connectivity. The ISP’s ASN handles that on the customer’s behalf.
An organisation only needs its own ASN when implementing BGP multi-homing, where the intention is to peer directly with multiple ISPs and advertise IP prefixes independently.
ASNs are assigned by Regional Internet Registries such as RIPE NCC in Europe, and obtaining one involves a formal application process and an ongoing annual fee.
Is BGP used to route traffic between cloud providers?
Yes, any traffic travelling between cloud providers crosses the public internet or dedicated interconnects, both of which are routed by BGP.
Major cloud providers such as AWS, Azure, and Google Cloud each operate their own Autonomous Systems with their own ASNs, peering directly with hundreds of networks globally.
This means they effectively run BGP multi-homing at a massive scale, with built-in redundancy and traffic engineering baked into their infrastructure.
Dedicated connectivity business offerings such as AWS Direct Connect, Azure ExpressRoute, and Google Cloud Interconnect bypass the public internet with a private link, but BGP still underpins the routing.
Will BGP affect the speed of an internet connection?
Not directly. BGP determines the path traffic takes across the internet, not the business broadband speed itself.
However, a poorly chosen BGP path, one that routes traffic through more hops than necessary or through congested networks, can increase latency and indirectly affect performance.
For most businesses on standard connectivity, BGP path selection is handled entirely by the ISP.
Organisations running BGP multi-homing can influence path selection themselves using attributes such as local preference and AS-path prepending.
Can a small business benefit from BGP multi-homing?
Not in most cases. BGP multi-homing requires an ASN, Provider Independent IP space, BGP-capable hardware, and peering agreements with two or more ISPs.
The cost and complexity of running this in-house are difficult to justify for most SMEs.
However, small businesses with genuinely critical connectivity needs can access the benefits indirectly through managed BGP services or cloud-delivered options such as Cloudflare Magic Transit, where the provider handles all the complexity on their behalf.

